Summarize the Content of the Blog
Key Takeaways
SOC Inefficiency Is a Strategic Risk: Splunk's State of Security 2025 found that 46% of security teams spend more time maintaining tools than defending the organization, and 59% are overwhelmed by too many alerts.
Splunk ES 8.x Is the Current-Gen SIEM Platform: Splunk Enterprise Security 8.4 (released January 2026) delivers unified TDIR workflows with AI assistance, risk-based alerting, UEBA, SOAR integration, and MITRE ATT&CK-mapped detections.
Risk-Based Alerting Cuts Through Alert Noise: Splunk ES risk-based alerting replaces alert-by-alert triage with consolidated risk notables, dramatically reducing the volume analysts must review each shift.
ITSI Bridges IT and Security: Splunk ITSI correlates service health scores with security events, giving SOC teams the operational context needed to prioritize incidents by real business impact.
AI Is Now Central to SOC Productivity: 59% of security professionals in Splunk's survey reported moderate to significant efficiency gains from AI. Splunk ES embeds an AI Assistant for Security that generates SPL queries and summarizes findings in natural language
Expert Implementation Is a Force Multiplier: The most common pitfalls in Splunk ES and ITSI deployments stem from poor data onboarding and incomplete configuration. A four-time Splunk Partner of the Year like bitsIO helps organizations avoid these gaps from day one.
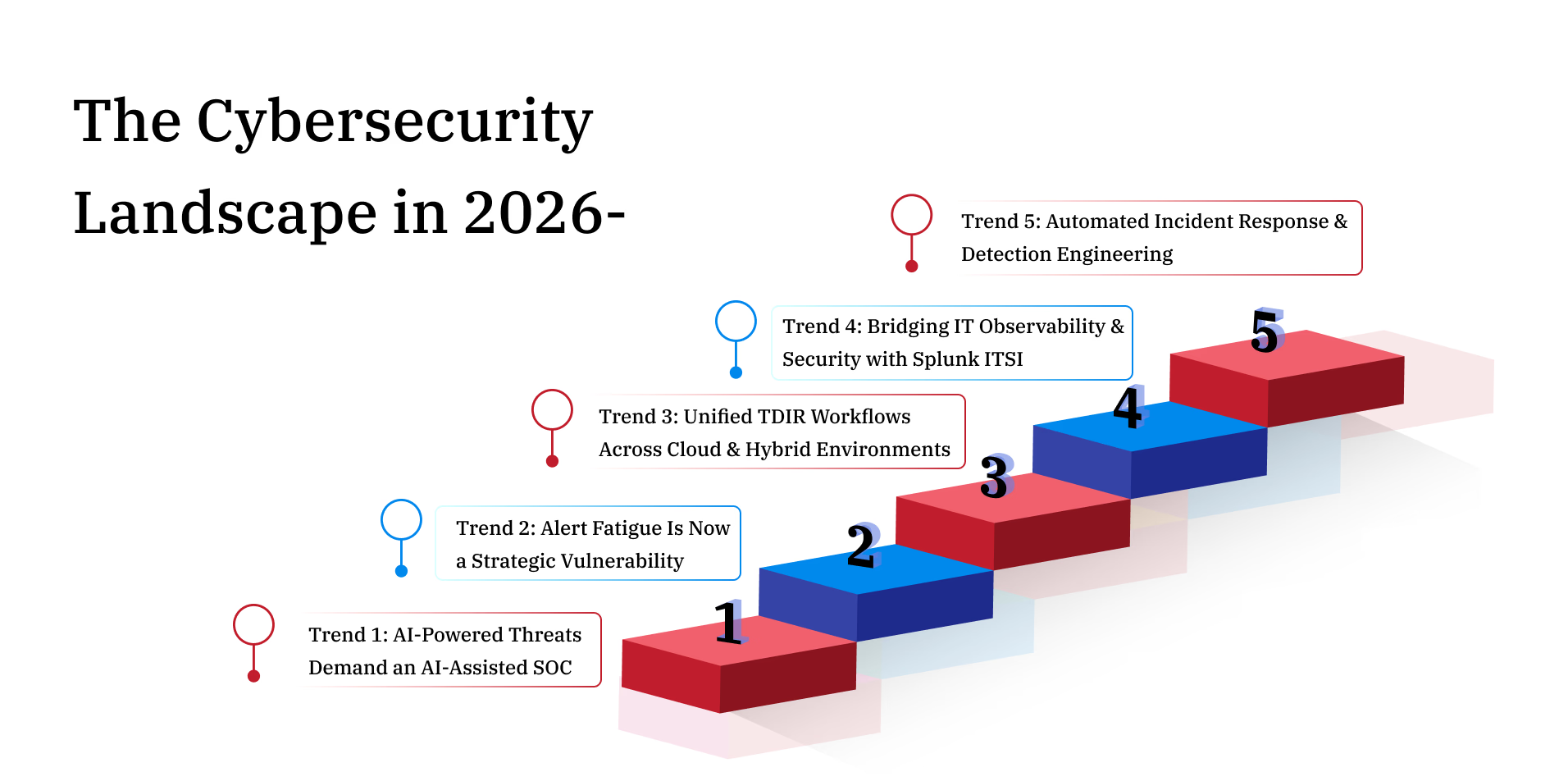
The Cybersecurity Landscape in 2026: Why SOC Teams Cannot Afford to Stand Still
Security operations teams are under more pressure than at any point in the industry's history. According to Splunk's State of Security 2025 report, which surveyed 2,058 security leaders across nine countries, 66% of organizations experienced a data breach in the past year alone.At the same time, 78% say their security tools are disconnected and dispersed, and 59% report having too many alerts to manage effectively[1].
Modern cybersecurity trends in 2026 are being shaped by three converging forces: AI-powered threats that evolve faster than traditional defenses, hybrid and multi-cloud infrastructure that expands the attack surface, and a widening skills gap that leaves SOC teams stretched thin. Addressing all three requires more than buying new tools. It requires a platform that unifies detection, investigation, and response across every layer of the environment.
This is where Splunk Enterprise Security and Splunk IT Service Intelligence (Splunk ITSI) deliver real, measurable value. This blog covers the most important cybersecurity trends shaping 2026, how these two Splunk products help security operations teams operationalize each one, and how bitsIO can accelerate your journey as a four-time Splunk Partner of the Year.
Trend 1: AI-Powered Threats Demand an AI-Assisted SOC
Threat actors are using AI to automate reconnaissance, craft convincing phishing campaigns at scale, and adapt malware to evade signature-based defenses in real time. Security teams that rely on manual processes or static detection rules will increasingly find themselves outpaced.
Splunk's research shows that applying AI to security workflows has become the highest cybersecurity priority for organizations in 2025, and 59% of those who have adopted AI report moderate to significant efficiency gains in their SOC.This is not enthusiasm for AI as a concept. It reflects practical results in real environments.
Splunk Enterprise Security 8.x, now at version 8.4 (released January 2026), embeds an AI Assistant for Security that enables analysts to generate and refine SPL searches using natural language. Analysts can describe what they need in plain English and receive working queries without manually writing complex search syntax.[2] In Splunk ES 8.2, the AI Assistant was extended to summarize individual findings in the analyst queue, reducing the time it takes to understand and prioritize each event.[3]
The result is an AI-driven SOC where human analysts focus on high-stakes decisions rather than routine triage, and where the platform itself handles the repetitive cognitive work that leads to burnout and missed detections.
Trend 2: Alert Fatigue Is Now a Strategic Vulnerability
The 2025 SANS Detection and Response Survey found that 73% of organizations rank false positives as their number one challenge in threat detection.[4] Separately, Splunk's own research shows that 55% of SOC teams are dealing with too many false positives, and 46% spend more time maintaining tools than actively defending the organization.When analysts cannot distinguish signal from noise, real threats slip through.
Splunk ES risk-based alerting (RBA) addresses this problem structurally. Rather than generating one alert per correlation rule match, RBA aggregates risk scores across users and entities over time. When the combined risk crosses a defined threshold, analysts receive a single high-confidence risk notice instead of dozens of individual alerts.
This approach means analysts spend their time on events that have already been evaluated by the platform for behavioral context and accumulated risk, rather than starting each investigation from scratch. Splunk ES 8.3 further enhanced this capability with Entity Risk Scoring, adding even finer-grained attribution of risk to specific entities within the environment.[5]
Trend 3: Unified TDIR Workflows Across Cloud and Hybrid Environments
Most organizations today operate across on-premises infrastructure, private cloud, and multiple public cloud providers. Security tools that were designed for a single-perimeter world create dangerous visibility gaps across this hybrid landscape.
With Splunk Enterprise Security 8.1, Splunk became the only vendor to deliver truly unified threat detection, investigation, and response (TDIR) workflows to both cloud and customer-managed on-premises deployments, including FedRAMP Moderate environments.[6] An independent IDC Business Value analysis sponsored by Splunk found that the unified TDIR platform increases security operations efficiency by 50%.
Splunk ES cloud security capabilities include deep integration with AWS, Azure, and GCP data sources, combined with MITRE ATT&CK-mapped detections that work consistently regardless of where the data originates. Splunk's Federated Analytics further extends this reach, allowing security teams to analyze data directly where it resides, including data in Amazon Security Lake, without requiring it to be moved into Splunk first.[7]
Trend 4: Bridging IT Observability and Security with Splunk ITSI
One of the most significant blind spots in security operations is the disconnect between IT service health and security events. A slowdown in a critical application, for example, might be the result of a misconfiguration, or it might be the early signature of a ransomware lateral movement campaign. Without correlating both views, analysts cannot tell the difference quickly enough.
Splunk ITSI fills this gap. Using predictive analytics and machine learning, Splunk ITSI models what a service's health will look like 30 minutes into the future, allowing teams to detect and respond before users experience impact.[9] Splunk ITSI's Event Analytics engine correlates related alerts into episodes and can reduce alert noise by more than 90% through machine learning-powered correlation and grouping.[10] When integrated with Splunk Enterprise Security, service health scores from ITSI feed directly into the security workflow, allowing analysts to see at a glance whether a security event is isolated or part of a broader service impact.
Splunk's research confirms the business case for this integration: 78% of organizations that share data between security and observability teams say it enables them to detect incidents faster, and 66% report quicker remediation as a result. Connecting Splunk ITSI and Splunk Enterprise Security operationalizes that insight by making it part of every analyst's daily workflow.
Trend 5: Automated Incident Response and Detection Engineering
Security teams are investing heavily in automated incident response to keep pace with attacker dwell times that are measured in hours rather than days. Splunk's research found that 59% of organizations believe adopting a unified platform has directly sped up incident response.
Splunk SOAR integrates directly with Splunk Enterprise Security through Mission Control, enabling analysts to trigger automated response playbooks from within the same investigation interface where they detected and analyzed the threat. Pre-built playbooks covering phishing investigation, malware containment, and threat intelligence enrichment reduce response times from hours to minutes, and the Visual Playbook Editor allows security teams to build and iterate on new playbooks without extensive coding.[8]
Detection engineering has emerged as a critical SOC capability in 2026. Splunk's State of Security 2025 found that 74% of security leaders rate detection engineering as the most important future skill for the SOC, and 63% want to use detection-as-code approaches frequently. Splunk Enterprise Security's Detection Studio and MITRE ATT&CK-aligned use case library give teams the foundation to build, version, and manage detections systematically across the full attack lifecycle.
How bitsIO Helps You Operationalize These Trends
As a four-time Splunk Partner of the Year with more than 300 enterprise clients and over 50 certified consultants operating across five countries, bitsIO brings the hands-on implementation expertise that transforms Splunk licenses into working security programs.
The most common failure mode in Splunk ES and ITSI deployments is not a technical limitation of the platform. It is incomplete data onboarding, undertrained risk scoring models, and services that were never properly modeled in ITSI. These gaps mean that even a fully licensed deployment produces noisy, low-confidence outputs that analysts learn to ignore.
bitsIO provides end-to-end implementation covering security data source onboarding and CIM normalization, risk-based alerting model configuration and tuning, ITSI service modeling aligned to business-critical applications, MITRE ATT&CK use case mapping, custom correlation search development, and SOAR playbook authoring. Managed Splunk security services are also available for organizations that need 24/7 coverage without building an internal team from scratch.
Ready to Build a More Resilient SOC?
Whether you are planning an initial Splunk Enterprise Security implementation, improving an existing deployment, or preparing to integrate Splunk ITSI with your security operations, bitsIO has the proven expertise to help. Schedule a consultation with the bitsIO team today.